Field producer Melissa Galvez speaks to Susan Crawford, Micah Sifry, Nicco Mele, and others to find out how the grassroots campaign to bring down SOPA/PIPA was built, and what it says about organizing on the internet.
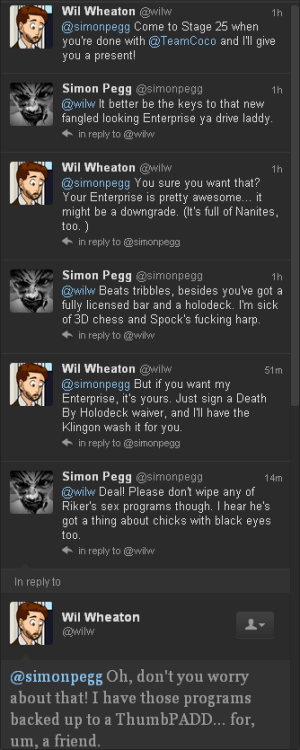
You guys, the cast of every single iteration of Star Trek is the best cast ever.
Trufax.
I still can’t believe that this is a real thing that happened.
Astronaut endorses destroying the moon!
The best exchange on the IAmA:
Ghostshirts it’s been a dream for a long time now, do you think that we’ll actually be able to blow up the moon in our lifetime?
RonGaran I truly believe that we can accomplish anything we set our minds on. We only need the will to do it
Eric Lawrence describes the new security features of IE10.
Do we have a word or phrase to describe the following situation: You code up something complicated and it compiles and works on the first try. You then spend the next ten minutes trying to figure out what's actually broken because it shouldn't be this easy.
Is this really the right way to do this? Feels icky:
To programmatically add or modify system environment variables, add them to the HKEY_LOCAL_MACHINE\System\CurrentControlSet\Control\Session Manager\Environment registry key, then broadcast a WM_SETTINGCHANGE message with lParam set to the string “Environment”.
Hmmm
“This rather embarrassing issue was pointed out to the committee, the fact that there were three votes too many, and that these three votes determined the outcome. When this was done, along with formally requesting a re-vote, that re-vote on the points in question was denied.”
By the URI RFC there is only one way to represent a particular IPv4 address in the host of a URI. This is the standard dotted decimal notation of four bytes in decimal with no leading zeroes delimited by periods. And no leading zeros are allowed which means there's only one textual representation of a particular IPv4 address.
However as discussed in the URI RFC, there are other forms of IPv4 addresses that although not officially allowed are generally accepted. Many implementations used inet_aton to parse the address from the URI which accepts more than just dotted decimal. Instead of dotted decimal, each dot delimited part can be in decimal, octal (if preceded by a '0') or hex (if preceded by '0x' or '0X'). And that's each section individually - they don't have to match. And there need not be 4 parts: there can be between 1 and 4 (inclusive). In case of less than 4, the last part in the string represents all of the left over bytes, not just one.
For example the following are all equivalent:
The bread and butter of URI related security issues is when one part of the system disagrees with another about the interpretation of the URI. So this non-standard, non-normal form syntax has been been a great source of security issues in the past. Its mostly well known now (CreateUri normalizes these non-normal forms to dotted decimal), but occasionally a good tool for bypassing naive URI blocking systems.
Set of issues run into by children using iPad apps. Should be generally appropriate though:
“Designing apps for children is extremely hard. Not only is quality, age-appropriate content hard to create, but designing the flow and interaction of these apps is made more difficult because designers must refrain from implementing advanced gestures, which would only confuse and frustrate kids (and, by extension, their parents). Yet all apps can and should adhere to certain basics. Hopefully, the four guidelines discussed here can become fixtures of all children’s apps.”
With Facebook changing its privacy policy and settings so frequently and just generally the huge amount of social sites out there, for many of us it is far too late to ensure our name doesn't show up with unfortunate results in web searches. Information is too easily copyable and archive-able to make removing these results a viable option, so clearly the solution is to create more data.
Create fake profiles on Facebook using your name but with a different photo, different date of birth, and different hometown. Create enough doppelgangers to add noise to the search results for your name. And have them share embarrassing stories on their blogs. The goal is to ensure that the din of your alternates drowns out anything embarrassing showing up for you.
Although it will look suspicious if you're the only name on Google with such chaff. So clearly you must also do this for your friends and family. Really you'll be doing them a favor.
Seems generally bad to embed sensitive info in the URI (the http+aes URI scheme’s decryption key) similar to the now deprecated password field.
Use case is covered here: http://lists.w3.org/Archives/Public/ietf-http-wg/2012JanMar/0811.html. Also discussion including someone mentioning the issue above.
Fascinating, but really most of the time it is in your code. Really you should look there first. Usually not the compiler’s fault, or the OS’s fault, or a loose wire in the CPU…
Patrick Desjardins is like a real life Connor Prikkel from For the Win. Quits his job to focus on his takeover of the virtual economy of the Star Wars MMO to make real money. Yes he was a Dark Jedi Master.

Follow the link for other great Al themed artwork.
(via http://twitter.com/alyankovic/statuses/177517595874951171)
Cursor spoofing. Great job!
I can’t believe the dumb TED conference made me miss seeing prominent Ragnarok denier Eliott Kalan being sprayed by with seltzer by Jon Stewart.